AWS credentials
Note
This feature is available in Lite, Enterprise, and Ultimate editions only.
DBeaver integrates with AWS authentication to let you securely access AWS-based services and cloud databases using IAM-based authentication.
Important
This guide assumes that required AWS resources and permissions - such as IAM roles, policies, or service settings are already configured on the AWS side. Learn more on required permissions.
Credential configuration¶
Choose the type of credentials by selecting the appropriate option from the Credentials dropdown menu.
Default credentials¶
Using Default credentials is the easiest way to integrate with various Single Sign-On (SSO) and web identity providers, as these providers typically supply credentials through configuration files.
To use Default credentials:
- Select Default credentials in the dropdown
- Enter the User and Region
- (Optional) Configure a Role name, AWS Secrets Manager, 3rd party account, or SSO.
Info
For information on individual fields, see the Credential settings section.
Tip
When you use Default credentials, AWS will then try to determine credentials by using the standard credential providers chain:
- Java system properties
- Environment variables
- Web identity token from AWS STS
- The shared credentials and config files
- Amazon ECS container credentials
- Amazon EC2 instance profile credentials
- Amazon SSO credentials
For a more detailed explanation, please refer to the AWS credentials documentation.
AWS Profiles¶
Use an AWS profile to authenticate with credentials stored in shared configuration files. For details, see AWS credentials config files documentation.
To use an AWS Profile:
- Select AWS Profile in the dropdown
- Choose your profile from the list
- (Optional) Configure a Role name, AWS Secrets Manager, 3rd party account, or SSO.
Info
For information on individual fields, see the Credential settings section.
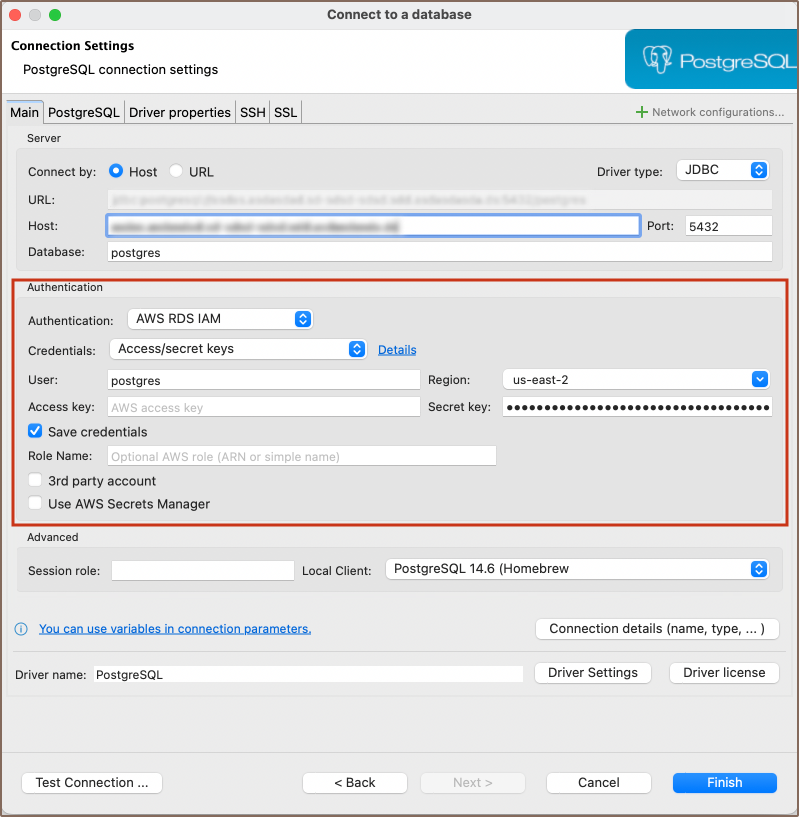
Access keys¶
Using the IAM user access key and secret key is the simplest way to authenticate. You just need to input these two keys. You have the option to save them locally for convenience, or, for better security, you can choose to enter them each time you connect to a database. For details, see official AWS guide.
To use Access keys:
- Select Access/secret keys in the dropdown
- Enter the Access key and Secret key
- (Optional) Configure a Role name, AWS Secrets Manager, or 3rd party account.
Info
For information on individual fields, see the Credential settings section.
User name/password¶
Use this option when AWS authentication is not required and the service or database expects direct credentials. This is a standard authentication method based on a user name and password, without IAM involvement.
To use User name/password:
- Select User name/password in the dropdown
- Enter the User and Password
- Select your Region
- (Optional) Configure a Role name, AWS Secrets Manager, or 3rd party account.
Info
For information on individual fields, see the Credential settings section.
Federated authorization¶
Use federated authorization to authenticate with AWS through an external identity provider.
To use federated authorization:
- Select Federated authorization in the dropdown
- Choose your provider in the FS plugin field (e.g., Okta, Microsoft Entra ID)
- Enter your User and Region
- (Optional) Configure a Role name.
Info
For information on individual fields, see the Credential settings section.
Credential settings¶
| Setting | Description |
|---|---|
| User | Your database or IAM user name. |
| Password | The database password (for User name/password method). |
| Region | The AWS region where your resource is located. |
| Access key | Your AWS IAM Access Key ID. |
| Secret key | Your AWS IAM Secret Access Key. |
| Session token | A temporary token required for session-based authentication. |
| Profile name | Name of the selected AWS profile from the shared credentials or config file. Used when AWS Profile is selected as the credentials type. |
| Role Name | The Amazon Resource Name (ARN) of the IAM role to assume. |
| FS plugin | The identity provider plugin for federated login: - Active Directory Federation Services - Microsoft Entra ID - Microsoft Entra ID SSO with MFA - Okta - PingFederate |
| Save credentials locally | Saves your password or keys in the secure storage. |
| Enable SSO | Enables AWS Single Sign-On for the selected credentials type. Learn more |
| 3rd party account | Enables access using a cross-account role or third-party ID. |
| Use AWS Secrets Manager | Enables retrieving database credentials from a secret at connection time. The secret must be created in advance in the same AWS region as your database. |
Tip
DBeaver also supports additional secure access options:
- AWS Systems Manager (SSM) for connecting to databases without exposing credentials. For information on setup, see AWS SSM setup guide.
- Cloud-based secret providers for retrieving database credentials at runtime. For information on configuration, see Secret Providers.

