Kerberos
Note
This feature is available in Lite, Enterprise, and Ultimate editions only.
DBeaver includes support for Kerberos authentication, enabling secure connections to your databases.

Kerberos authentication is a secure method for verifying user identities over non-secure networks. It is widely used in various environments, especially in database management systems, to ensure that communication between the client and server remains encrypted and authenticated.
This guide is designed to help you configure Kerberos authentication on the client machine, where DBeaver is installed. It assumes that the Kerberos Key Distribution Center (KDC) and the necessary server configurations have already been completed.
Supported databases¶
- AlloyDB
- Cockroach
-
Note
Kerberos authentication is only supported with version 11.x of the Db2 driver.
-
EnterpriseDB (EDB)
- Fujitsu
- Greenplum
- HANA
- MariaDB
- MySQL
- Oracle
- PostgreSQL
- PrestoDB
- PrestoSQL
- Redshift
- Teradata
- TimescaleDB
- Trino
- Yellowbrick
- YugabyteDB
Settings¶
The table below lists the basic settings required for Kerberos authentication in DBeaver. These settings are essential for establishing a secure connection to your database using Kerberos, providing user identification, authentication, and access control.
| Setting | Description |
|---|---|
| Username | Specifies the name of the user or role within the database. This is the identity under which you will connect to your database. |
| Kerberos user | A unique identity in the Kerberos system to which Kerberos can assign tickets, enabling access to services that are Kerberos-aware. |
| Realm | The domain over which a Kerberos authentication server can authenticate users, hosts, or services. It's often the uppercase version of the DNS domain name it oversees. |
| KDC Server | The hostname of your Kerberos Key Distribution Center (KDC), which is a service that provides session tickets and keys within an Active Directory domain. |
| Password | The password associated with your Kerberos user. This method involves directly entering your password. It's a simple, manual process suitable for environments where automated authentication methods are not preferred or available. |
Below are additional Kerberos authentication settings for advanced configuration:
| Extra configuration | Description |
|---|---|
| Use kinit | Uses an existing Kerberos ticket created with kinit. DBeaver reads credentials from the ticket cache (ccache). Make sure the cache contains a valid ticket and that its location matches what you configured. The kinit command is not run by DBeaver. |
| Use keytab | A checkbox option for those who prefer to use a keytab file instead of manually entering a password. Selecting this option also makes the Password field inactive because the keytab file contains encrypted keys that the Kerberos system uses for authentication. |
| Custom krb5.conf | Allows you to specify the path to your local Kerberos configuration file. This file contains settings that define the Kerberos realms, KDCs, and other parameters for your environment. |
| Debug Kerberos Connection | A checkbox that, when selected, enables the logging of detailed Kerberos connection information in your log files. |
Note
Some settings may be stored in a session cache. If you have updated the settings and still encounter connection issues, restarting DBeaver might be necessary to apply the changes effectively.
Extra configuration¶
The Extra configuration section within DBeaver's connection settings offers advanced options for customizing the
Kerberos. This section allows users to specify detailed settings, such as the use of a keytab file, kinit commands, or
a custom krb5.conf/krb5.ini file.
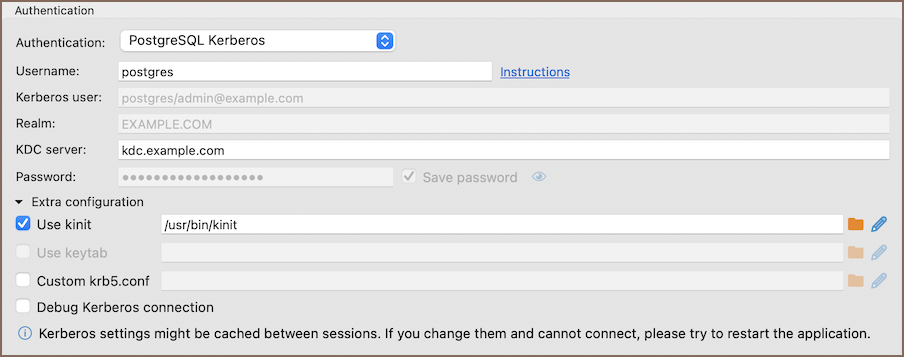
Using the kinit¶
The kinit command is a utility Kerberos provides to obtain and cache an initial ticket-granting ticket (TGT).
In the context of using DBeaver, the kinit command streamlines the authentication process by obtaining and caching an
initial ticket-granting ticket (TGT). This mechanism enables users to authenticate against Kerberos-enabled services,
reducing the need for continuous password inputs during the session.
To configure Kerberos authentication using kinit command, follow these steps:
- Make sure you have a valid Kerberos ticket-granting ticket (TGT), which can be obtained using the
kinitcommand. For a detailed guide, refer to the official documentation onkinitcommand. - Specify the path to your
kinittool in the Extra Configuration section in the Use kinit field. - Try connecting to your database. With these settings, DBeaver will use the
kinitcommand for authentication.
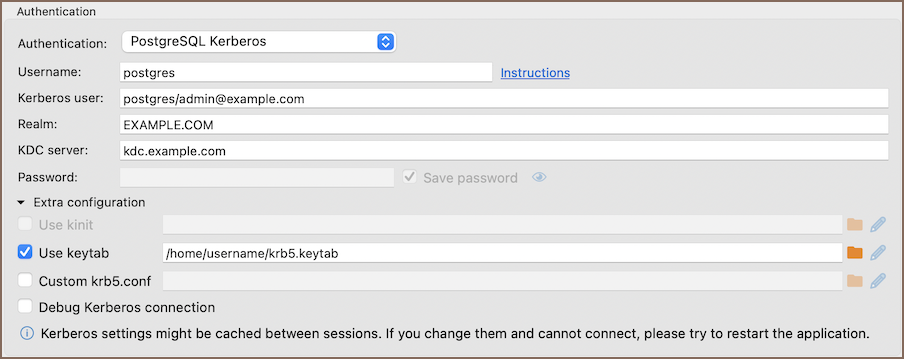
Using the keytab file¶
A keytab is a file containing pairs of Kerberos principals and encrypted keys derived from the Kerberos password. It enables authentication to various remote systems using Kerberos without entering a password.
In the context of using DBeaver, the keytab file simplifies the authentication process by requiring the user to provide all necessary credentials except the password.
To configure Kerberos authentication using a keytab file, follow these steps:
- Utilize the
ktutilcommand-line utility to generate a keytab file. This involves adding entries for your principals along with their encrypted keys. For comprehensive instructions on creating a keytab file, consult the official IBM documentation on creating a Kerberos principal keytab file. - Specify the path to your keytab file in the Extra Configuration section in the Use keytab field.
- Attempt to connect to your database. DBeaver will utilize the specified keytab file for authentication.
Windows specifics¶
On Linux and macOS, kinit and keytab files are supported natively. However, Windows does not support these
functionalities natively. To enable these features, Windows users need to install additional software.
A key tool for Windows users is MIT Kerberos for Windows. It allows the use
of kinit and provides utilities for managing keytab files, bridging the gap between Windows and Kerberos
authentication standards.
Local Kerberos configuration file¶
If you have a custom Kerberos configuration file (krb5.conf/krb5.ini), input the complete file path in the Custom
krb5.conf field.
The configuration file includes necessary configuration details such as KDCs and admin server locations for Kerberos realms, default values for the current Realm, and hostname to Kerberos realm mappings. If a custom configuration file path is provided, it is not necessary to fill in the standard authentication fields, as the configuration file contains all the required information.
Additional settings¶
When configuring PrestoSQL and Trino connections, especially in environments that utilize Kerberos authentication and SSL, certain additional settings might be necessary for connection:
| Setting | Description |
|---|---|
| Service name | Add the Kerberos service name of the remote coordinator. |
| Use SSL from JKS | Check this setting and manually add the file path to your .jks file if you need an SSL certificate from a JKS file. This is useful when the server's SSL certificate is not automatically trusted. If your JKS file is password-protected, add the password to the SSL JKS Password field to allow database to access the keystone. |
| SSL JKS Password | For additional security, the JKS file is password-protected. Add the password to the "SSL JKS" field to allow database to access the keystone. |
Troubleshooting¶
Oracle JDBC driver and Kerberos authentication¶
When configuring Kerberos authentication for Oracle databases, it is important to be aware of compatibility issues with certain JDBC driver versions. Specifically, Oracle JDBC driver version 21 has been known to cause issues with Kerberos authentication, often not working with older configurations.
To ensure Kerberos authentication functions properly with Oracle databases, it is recommended to use an older version of the Oracle JDBC driver. Versions 12.x or 19.x are known to be compatible and should be used for Kerberos authentication. By selecting one of these older driver versions, you can avoid the authentication problems introduced in version 21.
Kerberos ticket cache mismatch¶
Kerberos authentication may fail if the application uses a different credential cache than the one containing your ticket.
Run klist to check which cache is in use, and make sure the same cache is configured in DBeaver.
Tip
On macOS, the default cache is often API:. If DBeaver does not use this cache, create a file-based
cache with kinit -c and configure DBeaver to use it. For information on Kerberos connection fields, see Settings.

